CYBER SECURITY PENETRATION TESTING
Our expert cyber security team will uncover any weaknesses that could be used to breach your IT infrastructure and exploit your business, using our CREST accredited cyber security penetration testing.
Cyber Attack Simulation – Internal & External Testing – CREST Accredited
KNOW YOUR ENEMY
Our team conducts managed cyber penetration tests by recreating and ethically using various cyber-attack tactics. Unlike a vulnerability scan, penetration tests cannot be fully automated. A specialist penetration tester is used to look at your IT defences through the eyes of a cyber-criminal and attempt to find new and innovative ways to breach your external and internal defences.
HOW OUR PENETRATION TESTING SERVICES KEEP YOU SAFE
External Pen Test
We pose as external attackers, identifying any weaknesses in your firewalls, line of business applications, email servers, domain name servers and much more.
Internal Pen Tests
Not all attacks start externally. We can simulate the actions of internal attackers, in order to identify any potential risks to your business of data theft, operational disruption, and more.

Phishing Simulations
Awareness is the best defence against phishing. We can help maintain vigilance by carrying out mock phishing campaigns at regular intervals to test your team.
Web Application Tests
Protect your web applications from cyber threats with our expert penetration testing, which simulates real-world attacks to identify vulnerabilities and provide insights needed to fortify your defences and ensure your data remains secure

Compliance Requirements
Organisations who need to comply with standards including PCI DSS and ISO 27001 must conduct penetration testing at least once a year.

Physical Security Audit
We'll identify and strengthen weak points in your facility, uncovering vulnerabilities and providing targeted protection strategies to ensure your property is fully prepared to prevent breaches and safeguard valuable assets
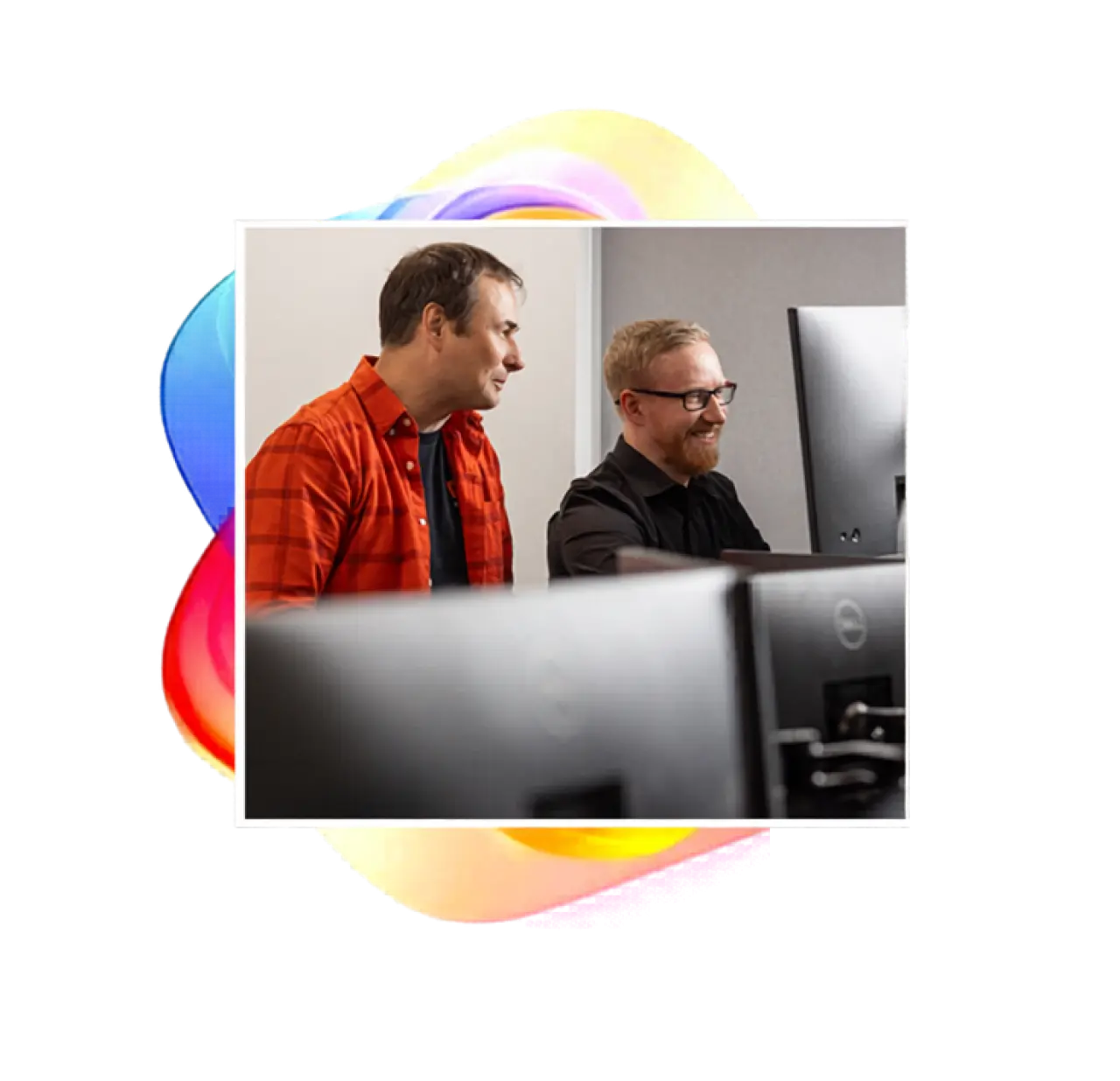
CYBER PENETRATION TESTING TESTIMONIALS
Whether you want to take a deeper, real-world approach to testing your security, or gain complete confidence that your defences can withstand targeted attacks, our penetration testing services are here to help.
Below, you’ll find videos of our clients sharing their experience of working with us and how we’ve helped strengthen their overall cybersecurity—giving them reassurance and the confidence to focus on what matters most.
Proactive IT Support
Clients from Mercat Tours, Eden Scott, and Cyber and Fraud Centre Scotland share how Consider IT’s reliable, secure, and people-focused IT support helps keep their organisations running smoothly.
Why Choose Consider IT
Kat from Mercat Tours, Ewan from Eden Scott, and Jude from Cyber and Fraud Centre Scotland explain why they trust Consider IT for dependable support, strong security, and a people-first partnership.
Seamless Onboarding with Consider IT
Kat, Ewan, and Jude share how Consider IT’s structured, stress-free onboarding makes transitioning to a new IT partner seamless and secure.
Test Your Defences Before Hackers Do
Book Your Pen Test Today.

CYBER PENETRATION TESTING FAQS
Penetration testing (often called a “pen test”) is a controlled, ethical attempt to hack into your systems, networks, or applications to identify vulnerabilities before a real attacker can exploit them.
It simulates real-world cyber attacks to uncover weaknesses such as misconfigurations, outdated software, or insecure user practices. The outcome is a clear report showing what was found, the level of risk, and how to fix it.
Penetration testing gives you a realistic view of how secure your business actually is - not just how secure you think it is.
It helps you to:
- Identify vulnerabilities before cyber criminals do
- Validate your existing security controls
- Meet compliance requirements (such as Cyber Essentials Plus)
- Protect sensitive data and maintain customer trust
- Reduce the risk of costly breaches and downtime
Without testing, vulnerabilities can remain hidden until they’re exploited.
Yes. Penetration testing is just one part of a strong cyber security strategy. You should also consider:
Vulnerability Scanning – Automated scans to regularly identify known weaknesses
Cyber Essentials Certification – A government-backed scheme covering key security controls
Cyber Essentials Plus – Includes hands-on technical verification of your security
Phishing Simulations – Tests how well your staff respond to social engineering attacks
Security Audits & Reviews – Broader assessments of your policies, processes, and configurations
A layered approach combining these services provides the best protection.
The cost of a penetration test varies depending on several factors, including the size and complexity of your environment.
Typical factors that affect pricing include:
-Number of systems, applications, or IP addresses
-Type of test (external, internal, web application, etc.)
-Depth and scope of testing required
-Level of reporting and remediation support
For an accurate quote, get in touch with us today.
WE'RE HERE TO HELP

CONTACT US
Want to see how your systems stand up to real-world attacks? Speak to our experts for trusted, in-depth testing.

GET A QUOTE
Looking for penetration testing tailored to your business? Want to know how managed services could help? Get a fast quote and understand where your risks lie.

CHECK YOUR CYBER HEALTH
Think your defences are strong? Run a quick check to see how you might perform under attack and where to improve.